[F1 [F2ANNEX I B U.K. REQUIREMENTS FOR CONSTRUCTION, TESTING, INSTALLATION AND INSPECTION
Textual Amendments
Appendix 10 GENERIC SECURITY TARGETS
VEHICLE UNIT GENERIC SECURITY TARGET U.K.
3. Product rationale U.K.
3.1. Vehicle unit description and method of use U.K.
The VU is intended to be installed in road transport vehicles. Its purpose is to record, store, display, print and output data related to driver activities.
It is connected to a motion sensor with which it exchanges vehicle's motion data.
Users identify themselves to the VU using tachograph cards.
The VU records and stores user activities data in its data memory, it also records user activities data in tachograph cards.
The VU outputs data to display, printer and external devices.
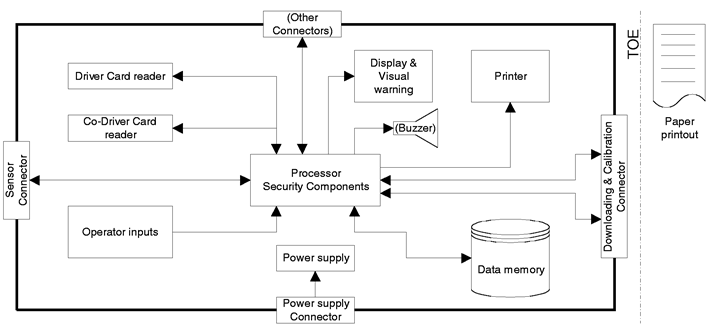
The vehicle unit's operational environment while installed in a vehicle is described in the following figure:
The VU general characteristics, functions and mode of operations are described in Chapter II of Annex I B.
The VU functional requirements are specified in Chapter III of Annex I B.
The typical VU is described in the following figure:
It must be noted that although the printer mechanism is part of the TOE, the paper document once produced is not.
3.2. Vehicle unit life cycle U.K.
The typical life cycle of the VU is described in the following figure:
3.3. Threats U.K.
This paragraph describes the threats the VU may face.
3.3.1. Threats to identification and access control policies U.K.
Users could try to access functions not allowed to them (e.g. drivers gaining access to calibration function)
Users could try to use several identifications or no identification.
3.3.2. Design related threats U.K.
Faults in hardware, software, communication procedures could place the VU in unforeseen conditions compromising its security
The use of non invalidated test modes or of existing back doors could compromise the VU security
Users could try to gain illicit knowledge of design either from manufacturer's material (through theft, bribery, …) or from reverse engineering
3.3.3. Operation oriented threats U.K.
Users could try to use mis-calibrated equipment (through calibration data modification, or through organisational weaknesses)
Users could try to modify data while exchanged between VU and tachograph cards (addition, modification, deletion, replay of signal)
Users could try to modify internal clock
Users could compromise the VU security through environmental attacks (thermal, electromagnetic, optical, chemical, mechanical, …)
Users could try to connect fake devices (motion sensor, smart cards) to the VU
Users could try to modify VU hardware
Users could try to modify the vehicle's motion data (addition, modification, deletion, replay of signal)
Users could use non activated equipment
Users could try to modify data output (print, display or download)
Users could try to defeat the VU security objectives by modifying (cutting, reducing, increasing) its power supply
Users could try to gain illicit knowledge of security data during security data generation or transport or storage in the equipment
Users could try to modify VU software
Users could try to modify stored data (security or user data).
3.4. Security objectives U.K.
The main security objective of the digital tachograph system is the following:
The data to be checked by control authorities must be available and reflect fully and accurately the activities of controlled drivers and vehicles in terms of driving, work, availability and rest periods and in terms of vehicle speed
Therefore the security objectives of the VU, contributing to the global security objective, are the following:
The data to be measured and recorded and then to be checked by control authorities must be available and reflect accurately the activities of controlled drivers and vehicles in terms of driving, work, availability and rest periods and in terms of vehicle speed
The VU must be able to export data to external storage media in such a way as to allow for verification of their integrity and authenticity.
3.5. Information technology security objectives U.K.
The specific IT security objectives of the VU contributing to its main security objectives, are the following:
The VU must control user access to functions and data
The VU must collect accurate accountability data
The VU must audit attempts to undermine system security and should trace them to associated users
The VU should authenticate users and connected entities (when a trusted path needs to be established between entities)
The VU must maintain stored data integrity
The VU must ensure that data output reflects accurately data measured or stored
The VU must ensure that processing of inputs to derive user data is accurate
The VU must provide a reliable service
The VU must secure data exchanges with the motion sensor and with tachograph cards.
3.6. Physical, personnel or procedural means U.K.
This paragraph describes physical, personnel or procedural requirements that contribute to the security of the VU.
3.6.1. Equipment design U.K.
VU developers must ensure that the assignment of responsibilities during development is done in a manner which maintains IT security
VU manufacturers must ensure that the assignment of responsibilities during manufacturing is done in a manner which maintains IT security, and that during the manufacturing process the VU is protected from physical attacks which might compromise IT security.
3.6.2. Equipment delivery and activation U.K.
VU manufacturers, vehicle manufacturers and fitters or workshops must ensure that handling of non activated VUs is done in a manner which maintains VU security
Vehicle manufacturers and fitters or workshops must activate the VU after its installation before the vehicle leaves the premises where installation took place.
3.6.3. Security data generation and delivery U.K.
Security data generation algorithms must be accessible to authorised and trusted persons only
Security data must be generated, transported, and inserted into the VU, in such a way to preserve its appropriate confidentiality and integrity.
3.6.4. Cards delivery U.K.
Tachograph cards must be available and delivered to authorised persons only
Drivers must possess, at one time, one valid driver card only
Card delivery must be traceable (white lists, black lists), and black lists must be used during security audits.
3.6.5. Recording equipment installation, calibration, and inspection U.K.
Installation, calibration and repair of recording equipment must be carried by trusted and approved fitters or workshops
Recording equipment must be periodically inspected and calibrated
Approved fitters and workshops must enter proper vehicle parameters in recording equipment during calibration.
3.6.6. Equipment operation U.K.
Drivers must play by the rules and act responsibly (e.g. use their driver cards, properly select their activity for those that are manually selected, …).
3.6.7. Law enforcement control U.K.
Law enforcement controls must be performed regularly and randomly, and must include security audits.
3.6.8. Software upgrades U.K.
Software revisions must be granted security certification before they can be implemented in a VU.] ]